The numeric sequence 185.63.2253.200(185.63.225.3.200) is often searched online by users who notice it in server logs, firewall alerts, analytics reports, or suspicious network activity. At first glance it appears to be an IP address, but technically the format does not follow the standard structure of valid IPv4 addresses. Understanding what this number represents and why it appears in searches can help users better manage network security, website monitoring, and server diagnostics.
In this guide, we explain what 185.63.2253.200 means, how IP addresses normally work, possible reasons it appears in logs, and security considerations for individuals and businesses in 2026.
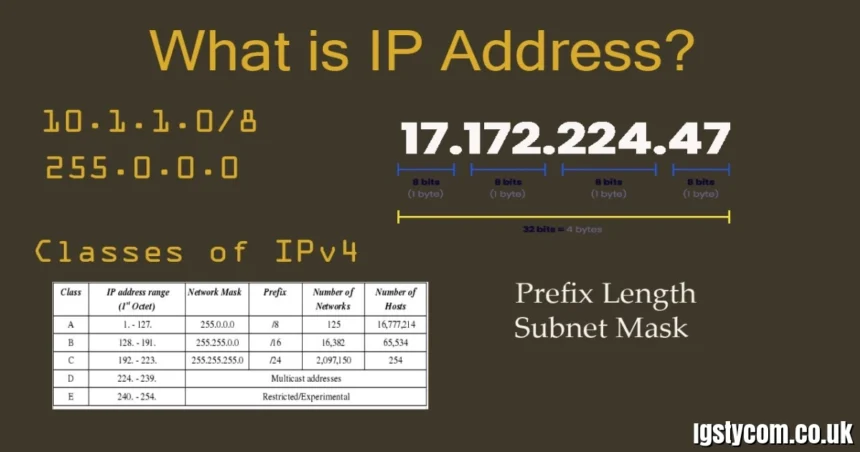
What Is an IP Address?
An IP address (Internet Protocol address) is a unique numerical identifier assigned to devices connected to a network. It allows computers, servers, and websites to communicate with each other across the internet.
Most systems today use two main formats:
- IPv4 – the traditional system using four numbers separated by dots
- IPv6 – a newer system using longer alphanumeric strings
Standard IPv4 Format
A typical IPv4 address looks like this:
192.168.1.1
Each section of the address is called an octet and must contain a value between 0 and 255.
Because of this rule, any number exceeding 255 cannot exist in a valid IPv4 address.
Why 185.63.2253.200 Is Not a Valid IPv4 Address
The sequence 185.63.2253.200 contains the number 2253, which exceeds the maximum allowed value of 255. This means it cannot be a legitimate IPv4 address.
Possible Reasons This Number Appears
There are several explanations for why users might encounter this number:
- Typing or formatting errors
- Malformed log entries
- Spam or bot-generated strings
- Scraped or corrupted data
For example, the correct address may have been:
- 185.63.225.200
- 185.63.223.200
A missing period or formatting issue can easily turn a legitimate IP into an invalid or confusing sequence.
Could It Be a Mistyped or Masked IP Address?
In many cases, strange numbers like 185.63.2253.200 appear because of typos or data formatting problems.
Common Causes
1. Missing Dot Separation
A legitimate IP such as:
185.63.225.200
may accidentally appear as:
185.63.225200
or another distorted variation.
2. Log File Parsing Errors
Some server monitoring tools or analytics systems combine characters incorrectly when exporting data.
3. Automated Bot Activity
Bots scanning websites may produce unusual or malformed IP formats that appear in logs but do not correspond to real devices.
Because of these possibilities, it is important to double-check raw server logs before assuming the number represents a real network address.
How to Investigate Suspicious IP Entries
If you encounter 185.63.2253.200 in network logs, the best approach is to verify whether it was caused by formatting issues or suspicious traffic.
Steps to Investigate
Check Raw Server Logs
Look at the original log entry to confirm whether the IP address was recorded correctly or altered by formatting.
Use IP Lookup Tools
If you suspect the real IP might be something like 185.63.225.200, you can analyze it using:
- WHOIS lookup tools
- IP reputation databases
- geolocation services
These tools reveal information such as:
- Hosting provider
- Country of origin
- Potential malicious activity reports
Monitor Repeated Activity
If similar numbers repeatedly appear in logs, it may indicate automated scanning attempts or bots targeting your server.
Security Risks Associated With Unknown IP Traffic
Even though 185.63.2253.200 itself is not a valid IP, suspicious entries in logs should still be taken seriously. Many cybersecurity incidents begin with unusual network requests or malformed data entries.
Possible Threats
- Automated vulnerability scanners
- Brute force login attempts
- Bot traffic targeting websites
- Malicious scraping tools
According to cybersecurity reports in 2025–2026, automated bots account for more than 40% of internet traffic, which means unusual entries in logs are common.
Monitoring tools such as firewalls, intrusion detection systems, and server analytics platforms can help detect suspicious behavior before it becomes a serious threat.
Best Practices for Network Monitoring in 2026
Maintaining strong network visibility and security monitoring is essential for website owners, system administrators, and businesses.
Recommended Practices
Use Advanced Log Monitoring
Tools like security information and event management (SIEM) systems help analyze unusual log entries and detect anomalies.
Enable Firewall Filtering
A properly configured web application firewall (WAF) can block suspicious traffic automatically.
Track IP Reputation
Use IP reputation databases to check whether incoming traffic originates from known malicious networks.
Maintain Updated Security Systems
Regular updates ensure that servers and applications remain protected from new vulnerabilities and automated attack tools.